Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities
Summary
Microsoft is aware of a new publicly disclosed class of vulnerabilities that are called “speculative execution side-channel attacks” that affect many modern processors and operating systems, including Intel, AMD, and ARM.
Note This issue also affects other operating systems, such as Android, Chrome, iOS, and MacOS, so we advise customers to seek guidance from those vendors.
Microsoft has released several updates to help mitigate these vulnerabilities. We have also taken action to secure our cloud services. See the following sections for more details.
Microsoft has yet not received any information to indicate that these vulnerabilities have been used to attack customers. Microsoft is working closely with industry partners including chip makers, hardware OEMs, and app vendors to protect customers. To get all available protections, hardware/firmware and software updates are required. This includes microcode from device OEMs and, in some cases, updates to antivirus software as well.
The following sections will help you identify and mitigate client environments that are affected by the vulnerabilities that are identified in
Microsoft Security Advisory ADV180002.
Windows Update will also provide Internet Explorer and Edge mitigations. And we will continue to improve these mitigations against this class of vulnerabilities.
Recommended actions
Customers must take the following actions to help protect against the vulnerabilities.
- Verify that you are running a supported antivirus application before you install OS or firmware updates. Contact the antivirus software vendor for compatibility information.
- Apply all available Windows operating system updates, including the January 2018 Windows security updates.
- Apply the applicable firmware update that is provided by the device manufacturer.
Windows-based machines (physical or virtual) should install the Microsoft security updates that were released on January 3, 2018. See
Microsoft Security Advisory ADV180002 for updates for the following versions of Windows.
| Operating System Version |
| Windows 10 (RTM, 1511, 1607, 1703, 1709) |
| Windows 8.1 |
| Windows 7 SP1 |

Warning
Customers who only install the Windows January 2018 security updates will not receive the benefit of all known protections against the vulnerabilities. In addition to installing the January security updates, a processor microcode, or firmware, update is required. This should be available through your device manufacturer.
Note Surface customers will receive a microcode update via Windows update.
 Surface updates for recent chip-related security vulnerability Surface - Windows 10 Forums
Surface updates for recent chip-related security vulnerability Surface - Windows 10 Forums
[FONT=&]How to get the January monthly update for Windows Update and Windows Update for Business with Group or MDM policy configurations set to disable preview builds[/FONT]
[FONT=&]
(Note This is not applicable to WSUS users.)
[/FONT]
[FONT=&]If you have currently disabled preview builds, then your organization’s devices will not be able to receive the January 2018 Windows security updates. The following Group or MDM policy configurations settings disable preview builds and will not allow the January 2018 Windows security updates. They will need to be changed to do so. To verify that you cannot receive the update, you can scan for available updates.
[/FONT]
| Group/MDM Configuration | Setting | Description |
| System/AllowBuildPreview | | Not allowed |
| “Toggle user control over Insider builds” | | Enabled |
| Update/ManagePreviewBuilds | 0 or 1 | Disable preview builds -or- Disable preview builds once next release is public |
| “Manage preview builds” | | Disable preview builds -or- Disable preview builds once next release is public |
[FONT=&]To allow devices to receive the January 2018 Windows security updates, you need to change the Group or MDM policies to the following “Not Configured” settings:
[/FONT]
| Group/MDM Configuration | Setting | Description |
| System/AllowBuildPreview | 2 | Not Configured |
| “Toggle user control over Insider builds” | | Not Configured |
| Update/ManagePreviewBuilds | 3 | Not Configured |
| “Manage preview builds” | | Not Configured |
[FONT=&]After devices have received the January 2018 Windows security updates, the policy configuration settings can be changed back to their previous state (disabling preview builds).[/FONT]
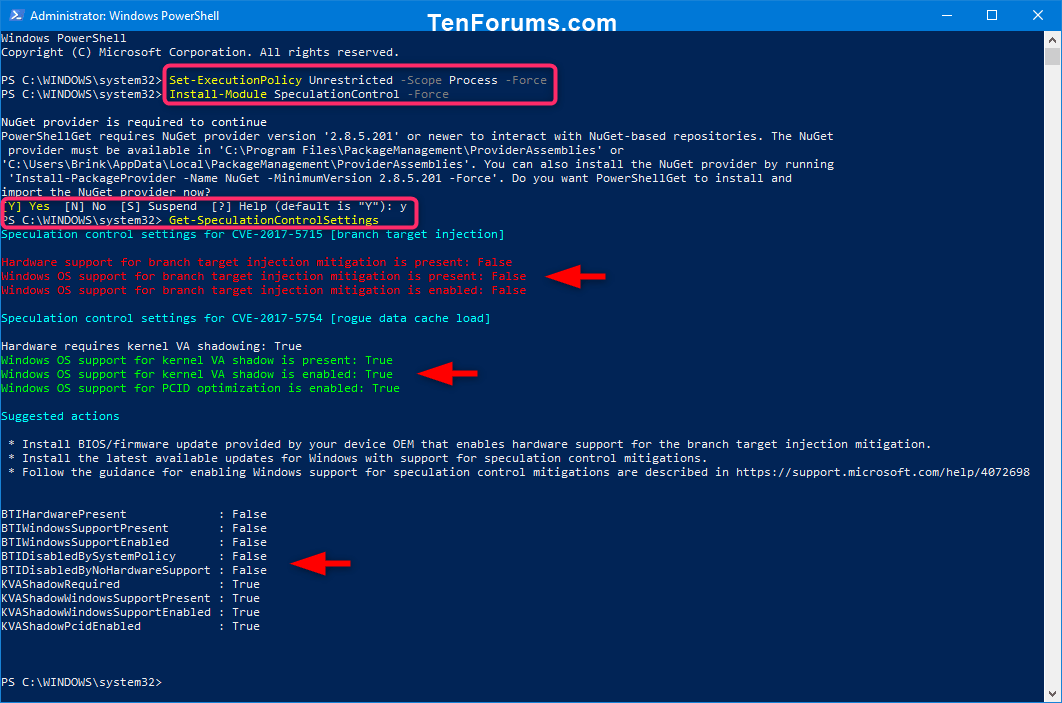
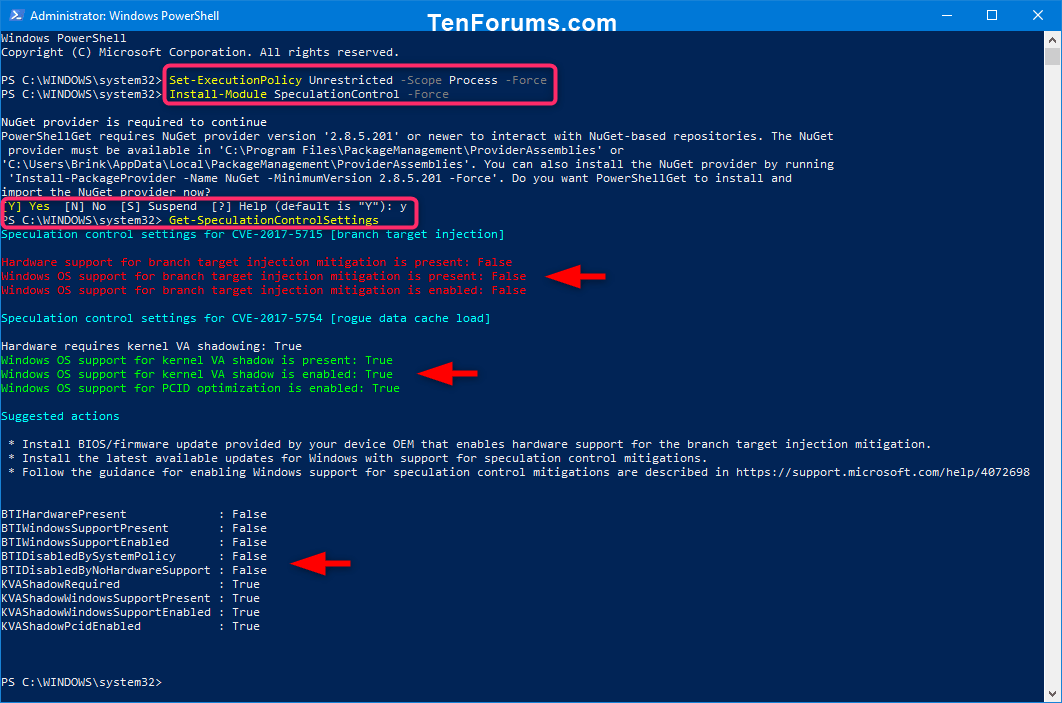
Verifying protections are enabled
To help customers confirm whether protections have been enabled, Microsoft has published a PowerShell script that customers can run on their systems. Install and run the script by running the following commands:
Note These verification steps only apply to Windows client and not to Azure instances. For further cloud guidance, see the
Azure blog.
| PowerShell Verification using the PowerShell Gallery |
1) Open elevated PowerShell.
2) Temporarily set PowerShell script execution policy
PS> Set-ExecutionPolicy Unrestricted -Scope Process -Force
3) Install the PowerShell module
PS > Install-Module SpeculationControl -Force
Type Y and press Enter if prompted to install and import NuGet.
4) Run the PowerShell module to validate protections are enabled
PS > Get-SpeculationControlSettings |
OR
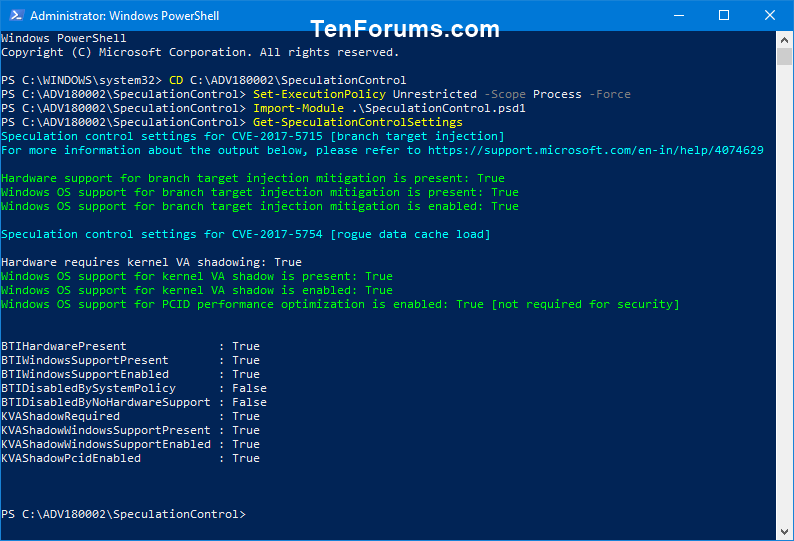
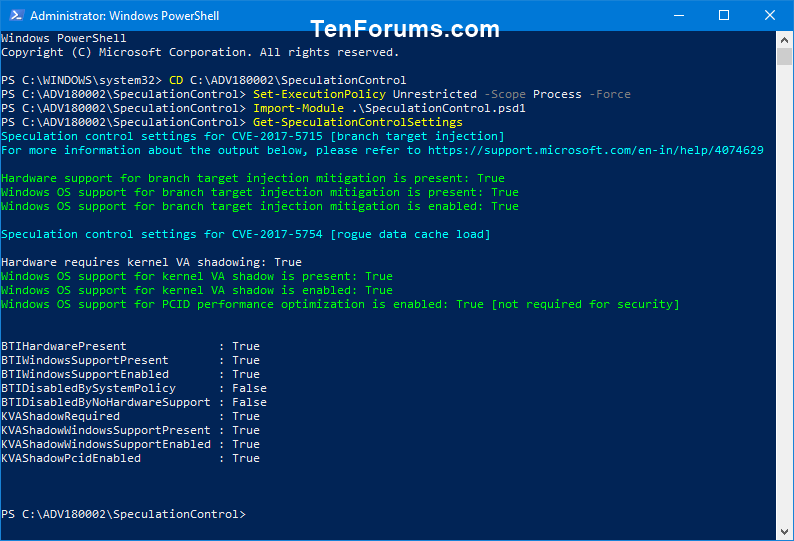
| PowerShell Verification using download from Technet |
1) Install PowerShell Module from Technet ScriptCenter
2) Open elevated PowerShell.
3) Switch to directory of extracted contents
PS> CD C:\ADV180002\SpeculationControl
4) Temporarily set PowerShell script execution policy
PS> Set-ExecutionPolicy Unrestricted -Scope Process -Force
5) Install the downloaded PowerShell module
PS > Import-Module .\SpeculationControl.psd1
6) Run the PowerShell module to validate protections are enabled
PS > Get-SpeculationControlSettings
|
The output of this PowerShell script will look like the following. Enabled protections will show in the output as “True”.
Code:
PS C:\> Get-SpeculationControlSettings
Speculation control settings for CVE-2017-5715 [branch target injection]
Hardware support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is enabled: True
Speculation control settings for CVE-2017-5754 [rogue data cache load]
Hardware requires kernel VA shadowing: True
Windows OS support for kernel VA shadow is present: True
Windows OS support for kernel VA shadow is enabled: True
Windows OS support for PCID optimization is enabled: True
 Switch | Registry Settings
Important
Switch | Registry Settings
Important This section, method, or task contains steps that tell you how to modify the registry. However, serious problems might occur if you modify the registry incorrectly. Therefore, make sure that you follow these steps carefully. For added protection, back up the registry before you modify it. Then, you can restore the registry if a problem occurs. For more information about how to back up and restore the registry, click the following article number to view the article in the Microsoft Knowledge Base:
322756 How to back up and restore the registry in Windows
Note By default, this update is enabled. No customer action is required to enable the fixes. We are providing the following registry information for completeness in the event that customers want to disable the security fixes related to CVE-2017-5715 and CVE-2017-5754 for Windows clients.
To enable the fix *
Code:
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverride /t REG_DWORD /d 0 /f
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverrideMask /t REG_DWORD /d 3 /f
Restart the computer for the changes to take effect.
To disable the fix *
Code:
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverride /t REG_DWORD /d 3 /f
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverrideMask /t REG_DWORD /d 3 /f
Restart the computer for the changes to take effect.
(There is no need to change MinVmVersionForCpuBasedMitigations.) |
* Note setting of 3 is accurate for both enable/disable settings due to masking.
Frequently asked questions
1.
How can I tell if I have the right version of the CPU microcode?
The microcode is delivered through a firmware update. Consult with the device manufacturer about the firmware version that has the appropriate update for your CPU.
2.
My operating system (OS) is not listed. When can I expect a fix to be released?
Addressing a hardware vulnerability through a software update presents significant challenges, and mitigations for older operating systems require extensive architectural changes. Microsoft is working with affected chip manufacturers to determine the best way to provide mitigations, which may be delivered in future updates.
3.
Where can I find Surface firmware/hardware updates?
Updates for Microsoft Surface devices will be delivered to customers through Windows Update along with the updates for the Windows operating system. For more information, see
KB 4073065.
If your device is not from Microsoft, apply firmware from the device manufacturer. Contact the manufacturer for more information.
4.
I have an x86 architecture but don’t see an update. Will I get one?
Addressing a hardware vulnerability through a software update presents significant challenges, and mitigations for older operating systems require extensive architectural changes. We are working with affected chip manufacturers to determine the best way to provide mitigations for x86 customers, which may be delivered in a future update.
Warning
Customers who only install the Windows January 2018 security updates will not receive the benefit of all known protections against the vulnerabilities. In addition to installing the January security updates, a processor microcode, or firmware, update is required. This should be available through your device manufacturer.Surface updates for recent chip-related security vulnerability Surface - Windows 10 Forums