MasterChief
Banned

- Messages
- 1,883
Source: Testosterone Pit - Home - LEAKED: German Government Warns Key Entities Not To Use Windows 8 ? Links The NSA
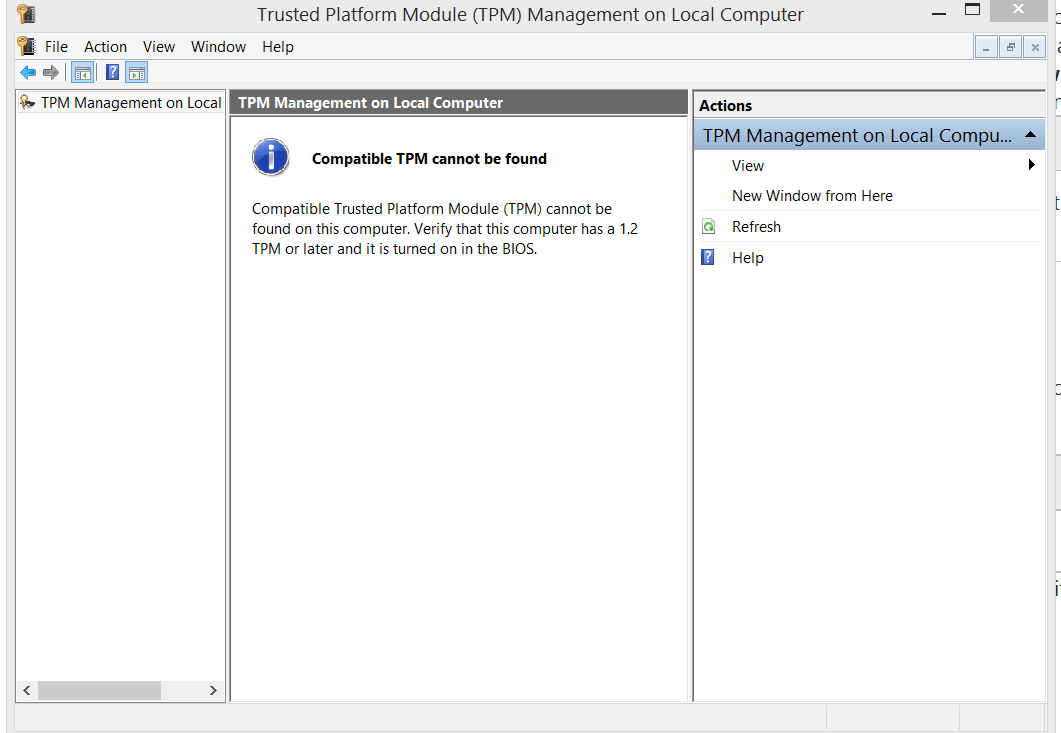
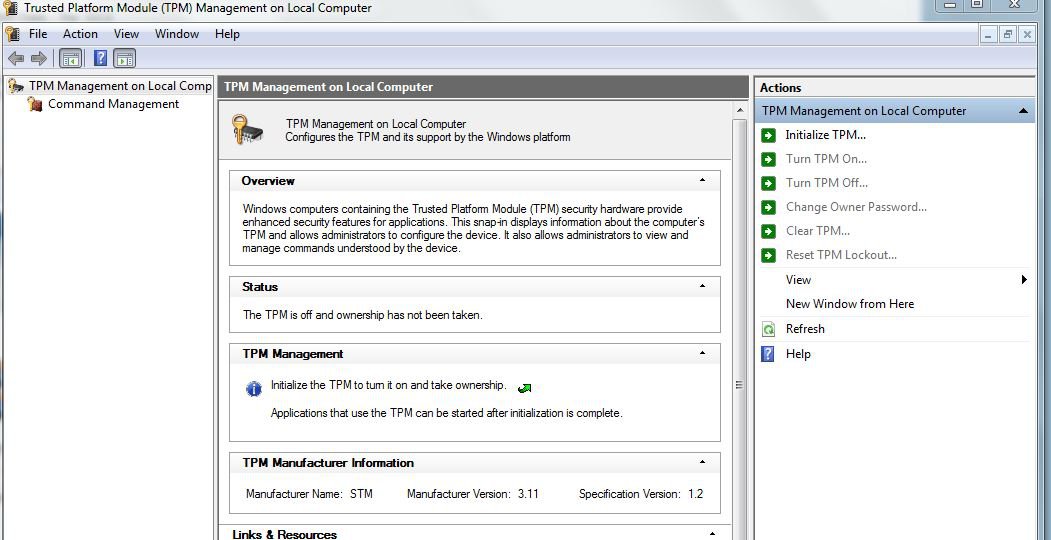
"The backdoor is called “Trusted Computing,” developed and promoted by the Trusted Computing Group, founded a decade ago by the all-American tech companies AMD, Cisco, Hewlett-Packard, IBM, Intel, Microsoft, and Wave Systems. Its core element is a chip, the Trusted Platform Module (TPM), and an operating system designed for it, such as Windows 8. Trusted Computing Group has developed the specifications of how the chip and operating systems work together.
Its purpose is Digital Rights Management and computer security. The system decides what software had been legally obtained and would be allowed to run on the computer, and what software, such as illegal copies or viruses and Trojans, should be disabled. The whole process would be governed by Windows, and through remote access, by Microsoft.
Now there is a new set of specifications out, creatively dubbed TPM 2.0. While TPM allowed users to opt in and out, TPM 2.0 is activated by default when the computer boots up. The user cannot turn it off. Microsoft decides what software can run on the computer, and the user cannot influence it in any way. Windows governs TPM 2.0. And what Microsoft does remotely is not visible to the user. In short, users of Windows 8 with TPM 2.0 surrender control over their machines the moment they turn it on for the first time."
"The backdoor is called “Trusted Computing,” developed and promoted by the Trusted Computing Group, founded a decade ago by the all-American tech companies AMD, Cisco, Hewlett-Packard, IBM, Intel, Microsoft, and Wave Systems. Its core element is a chip, the Trusted Platform Module (TPM), and an operating system designed for it, such as Windows 8. Trusted Computing Group has developed the specifications of how the chip and operating systems work together.
Its purpose is Digital Rights Management and computer security. The system decides what software had been legally obtained and would be allowed to run on the computer, and what software, such as illegal copies or viruses and Trojans, should be disabled. The whole process would be governed by Windows, and through remote access, by Microsoft.
Now there is a new set of specifications out, creatively dubbed TPM 2.0. While TPM allowed users to opt in and out, TPM 2.0 is activated by default when the computer boots up. The user cannot turn it off. Microsoft decides what software can run on the computer, and the user cannot influence it in any way. Windows governs TPM 2.0. And what Microsoft does remotely is not visible to the user. In short, users of Windows 8 with TPM 2.0 surrender control over their machines the moment they turn it on for the first time."
My Computer
System One
-
- OS
- 7601.18247.x86fre.win7sp1
- Computer type
- PC/Desktop
- System Manufacturer/Model
- Self-built Intel based
- CPU
- Pentium D 925 3.0 GHz socket 775, Presler @ ~ 3.2 GHz
- Motherboard
- Intel DQ965MT
- Memory
- Hyundai 2 GB DDR2 @ 333 MHz
- Graphics Card(s)
- ASUS DirectCU II HD7790-DC2OC-2GD5 Radeon HD 7790 2GB 128-Bit GDDR5
- Sound Card
- MOTU Traveler firewire interface
- Hard Drives
- 1 Seagate Barracuda SATA II system/boot drive 80 GB, 2 Western Digital hdds - 1 is SATA II Caviar Black 1 TB attached to card (assorted media, page, temp), other is SATA I 420 GB (games, media, downloads)
- PSU
- Thermaltake 450W
- Cooling
- stock Gateway cooling, extra large fan in rear of case
- Keyboard
- Alienware/Microsoft Internet kb
- Mouse
- Logitech M510
- Internet Speed
- Optimum Online, fast for US
- Browser
- Pale Moon
- Antivirus
- Kaspersky integrated into ZoneAlarm+Antivirus